Every modern business depends on software in some way. Customers use apps to shop, book services, manage finances, learn online, store documents, communicate with teams, and access healthcare services. This means software applications are now handling more user data than ever before.
Because of this, secure and compliant applications have become a fundamental business requirement. Users want to know that their information is safe. Businesses want to avoid data leaks, legal problems, and loss of trust.
A good application should not only be fast and user-friendly. It should also be secure, reliable, and designed with privacy in mind. This is especially important for SaaS platforms, healthcare apps, finance tools, education software, eCommerce platforms, and enterprise systems.
Why Security Is No Longer Optional
In the early stage of app development, many founders focus only on features — dashboards, user profiles, payments, reports, and mobile screens. Security is often pushed to the end. This is a dangerous approach.
If security is ignored in the beginning, the product may develop weak points that become difficult to fix later. Poor password handling, weak access control, insecure APIs, exposed files, and missing validation can create serious problems. A single security issue can damage a company’s reputation — users may stop trusting the product, clients may cancel contracts, and investors may question the product’s maturity.
Security should be part of the foundation, considered during planning, design, development, testing, deployment, and maintenance. This is also why making the right tech stack choices for your startup app must include evaluating security capabilities from the start.
Compliance Builds Business Trust
Compliance means following rules, standards, or legal requirements related to data protection, privacy, security, and industry practices. Finance applications may need strong transaction security. Healthcare applications may need privacy controls for patient information. Education platforms may need safe student data handling.
Even when formal compliance is not required in the early stage, following good security practices helps build trust. A business client may ask whether the application has user roles, activity logs, backups, encryption, and secure hosting. Compliance is not only about passing audits — it is about showing users and clients that the application is serious about protecting data.
Security should be part of the foundation, considered during planning, design, development, testing, deployment, and maintenance. This is also why making the right tech stack choices for your startup app</a> must include evaluating security capabilities from the start.
User Data Has Become More Sensitive
Many applications collect personal and business information — names, email addresses, phone numbers, payment details, addresses, uploaded documents, health records, messages, location data, and business reports. If this data is not protected, users can be harmed through identity misuse, exposed private information, or disrupted business operations.
Good software should collect only the data that is needed. It should clearly separate user permissions, protect sensitive records, and ensure data is not accidentally exposed through APIs, logs, or public links.
Role-Based Access Control Is Essential
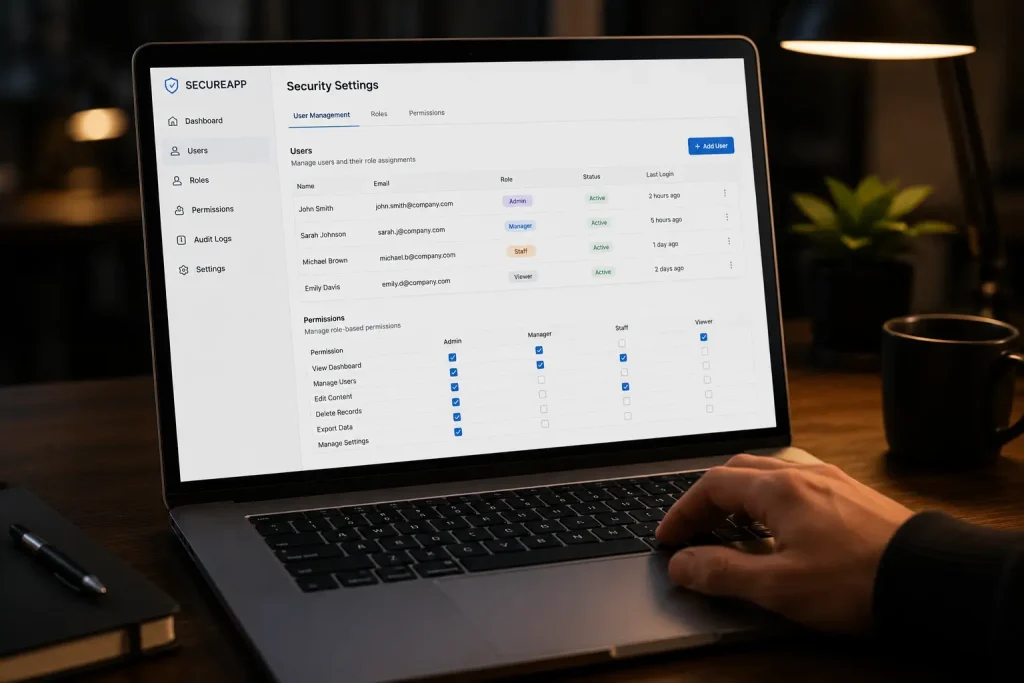
One of the most important parts of secure application development is role-based access control. Not every user should be able to see or change every piece of information. In a SaaS product, the account owner may manage billing while a team member may only use product features. In a school management system, teachers, students, parents, and admins should have different access levels.
Role-based access control helps prevent accidental misuse and unauthorized access. It also makes the application more suitable for businesses because companies usually have teams with different responsibilities. This feature is also one of the ten core requirements of any modern SaaS application.
Secure APIs Protect the Entire Product
Most modern applications depend on APIs for web apps, mobile apps, admin panels, and third-party integrations. If APIs are not secure, the entire product is at risk. Secure APIs should include authentication, authorization, request validation, rate limiting, proper error handling, and logging.
The API should not expose unnecessary data. A normal user should not be able to access admin-level data by changing an ID in the API request. True security must be enforced in the backend — a good frontend improves user experience, but it cannot substitute for proper backend access controls. For a detailed look at API design, see our article on how API-first development is transforming modern software.
Audit Logs and Activity Tracking
Audit logs record important actions inside the system — when a user logs in, creates a record, updates information, deletes a file, changes permissions, downloads a report, or performs an admin action. This helps businesses understand what happened inside the application and investigate mistakes or suspicious activity.
Audit logs are especially important in industries like healthcare, finance, legal services, and enterprise software where organizations may need to prove who accessed what information and when. For growing SaaS products, audit logs can also become a premium feature for business customers.
Data Backup and Recovery Planning
Security is not only about preventing attacks. It is also about recovering from problems. Applications may face server failures, accidental deletion, database corruption, human error, or cyberattacks. Without proper backups, a business may lose important data.
A secure application should have a backup strategy — regular, tested, and safely stored. The team should also know how to restore data when needed. For serious business applications, disaster recovery planning is also important. This means having a clear process to bring the system back online after a major failure.

Security in Healthcare and Sensitive Industries
Some industries need stronger security because the data is highly sensitive. A healthcare application may manage patient profiles, doctor notes, prescriptions, diagnostic reports, appointment history, billing details, and medical documents. This type of data must be handled carefully.
Healthcare platforms should be built with strong access control, secure storage, audit logs, privacy controls, and reliable infrastructure. Businesses planning medical software often work with a specialized healthcare software development company to build secure and scalable healthcare technology solutions. The same thinking applies to finance, insurance, education, and legal services — security must match the level of risk.
Security Can Become a Competitive Advantage
Many founders see security as a cost. But security can also become a selling point. Business customers are more likely to trust software that has strong security practices. Enterprise clients often ask security questions before buying a SaaS product. When a product can clearly explain its security features, it becomes more professional and gives confidence to customers, partners, and investors.
Conclusion
The demand for secure and compliant applications is growing because software now handles important personal and business data. Users expect privacy. Businesses expect reliability. Industries expect proper controls. A modern application must be designed to protect information from the beginning.
For indie developers, startups, software companies, and internet entrepreneurs, security should not be seen as a barrier. It should be seen as a foundation for trust and growth. Every software idea has the potential to become a valuable product. When that idea is supported by secure architecture, responsible data handling, and compliance-ready planning, it can grow into software that users trust, businesses depend on, and markets respect.
Published on www.appsmamma.com











